Note
Defender for Identity standalone sensors do not support the collection of Event Tracing for Windows (ETW) log entries that provide the data for multiple detections. For full coverage of your environment, we recommend deploying the Defender for Identity sensor.
The following steps walk you through the process for validating that port mirroring is properly configured. For Defender for Identity to work properly, the Defender for Identity standalone sensor must be able to see the traffic to and from the domain controller. The main data source used by Defender for Identity is deep packet inspection of the network traffic to and from your domain controllers. For Defender for Identity to see the network traffic, port mirroring needs to be configured. Port mirroring copies the traffic from one port (the source port) to another port (the destination port).
Validate port mirroring using Net Mon
- Install Microsoft Network Monitor 3.4 on the Defender for Identity standalone sensor that you want to validate.
Important
If you choose to install Wireshark in order to validate port mirroring, restart the Defender for Identity standalone sensor service after validation.
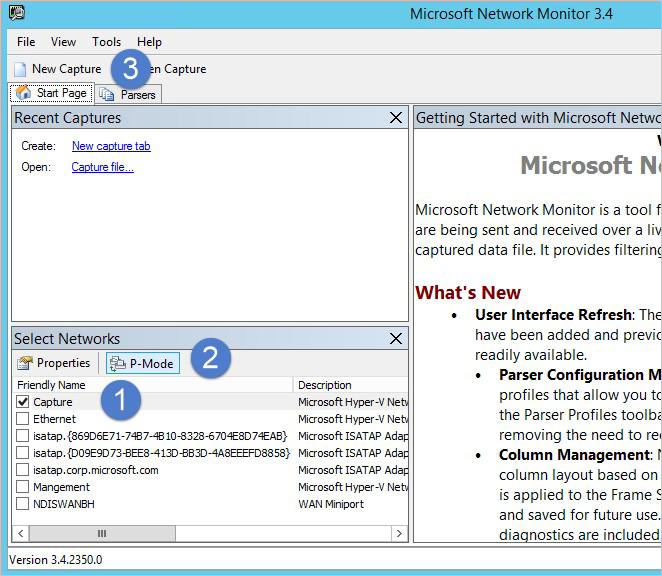
- Open Network Monitor and create a new capture tab.
- Select only the Capture network adapter or the network adapter that is connected to the switch port that is configured as the port mirroring destination.
- Ensure that P-Mode is enabled.
- Click New Capture.
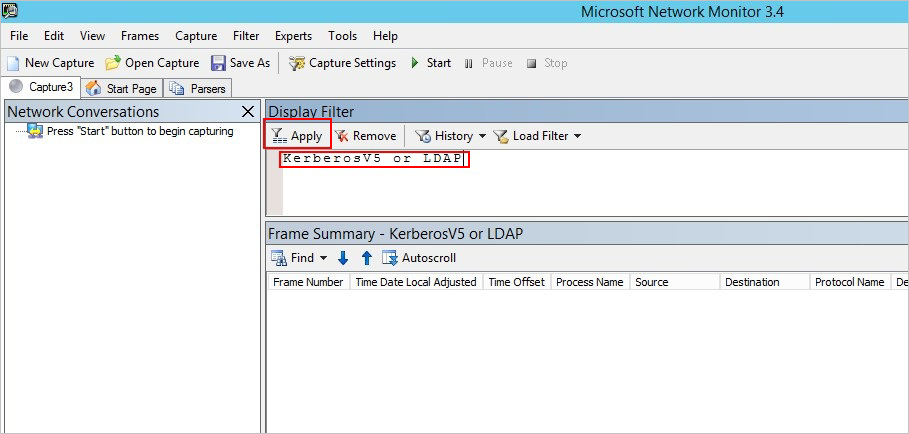
- In the Display Filter window, enter the following filter: KerberosV5 OR LDAP and then click Apply.
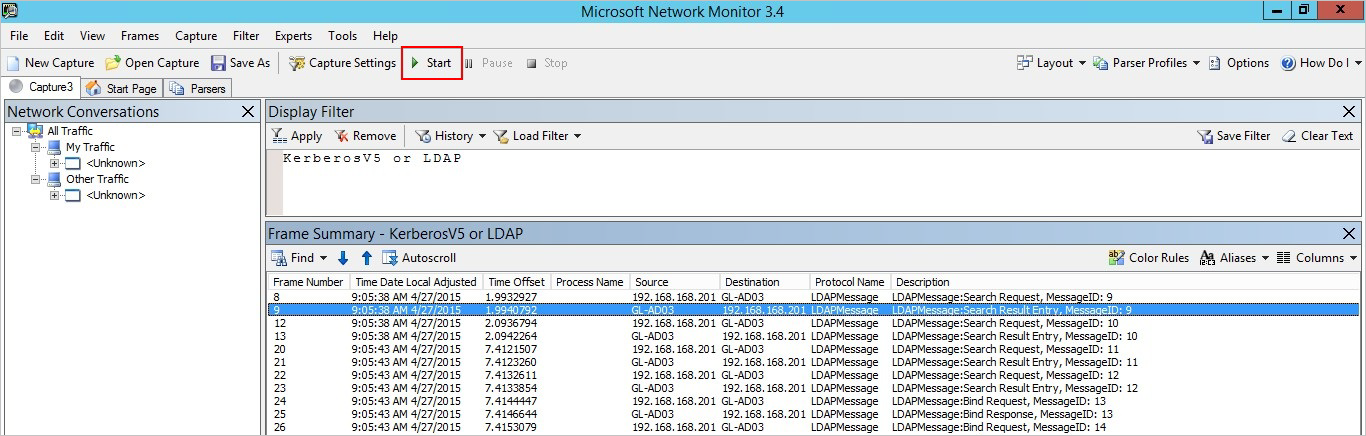
- Click Start to start the capture session. If you do not see traffic to and from the domain controller, review your port mirroring configuration.
Note
It is important to make sure you see traffic to and from the domain controllers.
- If you only see traffic in one direction, work with your networking or virtualization teams to help troubleshoot your port mirroring configuration.

