Applies to: Sophos Home Premium and Free (Mac)
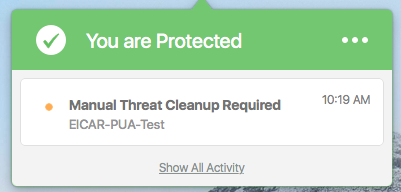
Why did I receive a Manual Threat Cleanup Required message?
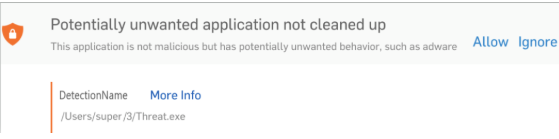
This message usually appears when Sophos Home detects a PUA, or when a file is contained inside a backup volume, external or disconnected drive, or inside a location Sophos Home does not have access to delete.
These detections are not automatically removed by Sophos Home but can be manually removed by following the scenarios below:
How to clean up threats manually – General approach
You can manually address threats via the Sophos Home shield, or by accessing the Sophos Home dashboard. See below for specific instructions, as well as different scenarios that may come up.
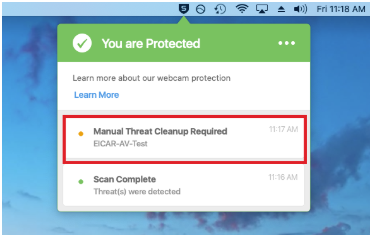
Addressing threats using the Sophos Home Shield
- Click on the detection via the Sophos Home Shield
- Click on the path to open it in Finder (or, if it doesn’t open, hover the mouse to see the full path, and open it using Spotlight)
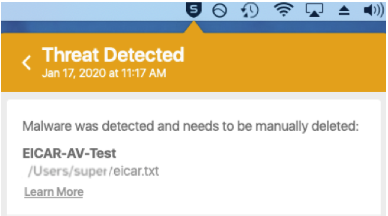
- Navigate to the file, right-click –> Move to trash
- On the Sophos Home Shield, select the manual clean up required entry and click Ignore, or close it with the X to acknowledge it
- Empty the trash
- Run a Full System scan to ensure no more detections are found.
What if the file is not found at the location?
This can happen when viewing hidden folders. I order to see files inside hidden folders, follow these steps:
Access the location where the file resides, using Finder
Once there, press Command+Shift+Dot (three keys, all the same time, the last one is “. ” an actual dot)
After deleting the offending file, press Command+Shift+Dot to hide the files again.
Addressing threats using the Sophos Home Dashboard
- Log in to your Sophos Home Dashboard and locate the affected system, click on it
- Click on HISTORY and locate the detection that requires manual clean up, it will show the full path, including file name, location and date.
- Open Finder and navigate to the path indicated in the dashboard
- Right-click on the file that is triggering the detection –> Move to Trash
- Empty the trash
- On the Sophos Home Dashboard find the manual clean up detection and choose Ignore
- Run a Full System scan
Detection is inside a Time Machine snapshot
If the detection is located inside a Time Machine snapshot, you’ll need to access Time Machine, find the date/time listed in the detection and delete the file inside Time Machine (right-click on file –> Delete all backups of <file> ). See the video and steps below:
IMPORTANT: Starting with macOS11 Big Sur, Apple has removed the ability to remove a single file from Time Machine. Instead, users can follow the below-listed instructions to remove the entire backup.
For further questions regarding this limitation, please reach out to Apple support.
Additional options from Apple regarding how to remove backups from Time Machine can be found here:
About Time Machine local snapshots (See section “How local snapshots use storage space”)
macOS 11 -Big Sur and macOS 12 -Monterey video instructions
IMPORTANT: Starting with macOS11 Big Sur, Apple has removed the ability to remove a single file from Time Machine. Instead, users can follow the below-listed instructions to remove the entire backup. For further questions regarding this limitation, please reach out to Apple support.
macOS 10.X versions – video instructions
Step-by-step instructions (does not apply to Big Sur)
Option 1 – Removing a Time Machine threat using the Sophos Home Shield
- Click on the Manual detection on the Sophos Home Shield
- Hover the mouse over the path to see its entirety
- Take note of the date/time and file name, for example:
/Volumes/<Time Machine Volume Name>/Backups.backupdb/<Computer Name>/YYYY-MM-DD-NNNNNN/<User Name>/…threatName
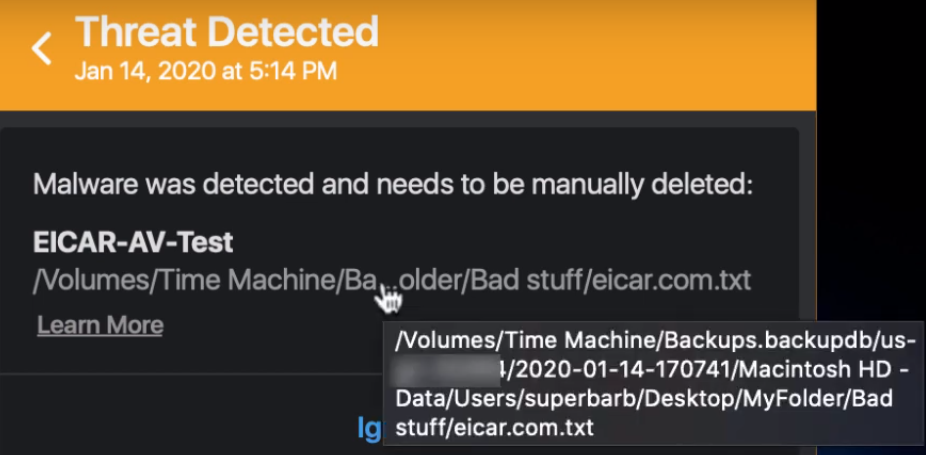
- Enter Time Machine on your Mac and navigate to the day/time that matches the threat, then locate the file
- Right click on the offending file and choose Delete All Backups of [file name] (Repeat this step for any other Time Machine offending items)
- Hit Esc to exit Time Machine
- On the Sophos Home Shield find the manual clean up detection and hit Ignore
- Run a Full System scan
Option 2 – Removing a Time Machine threat via the Sophos Home Dashboard
- Log in to your Sophos Home Dashboard and locate the affected system, click on it
- Click on HISTORY and locate the detection that requires manual clean up, it will show the full path, including file name, location and date. For example, /Volumes/<Time Machine Volume Name>/Backups.backupdb/<Computer Name>/YYYY-MM-DD-NNNNNN/<User Name>/…threatName
- Enter Time Machine on your Mac and navigate to the day/time that matches the threat, then locate the file
- Right-click on the offending file and choose Delete All Backups of [file name] (Repeat this step for any other Time Machine offending items).
- Hit Esc to exit Time Machine
- On the Sophos Home Dashboard find the manual clean up detection and choose Ignore
- Run a Full System scan
Detection is inside an Email attachment
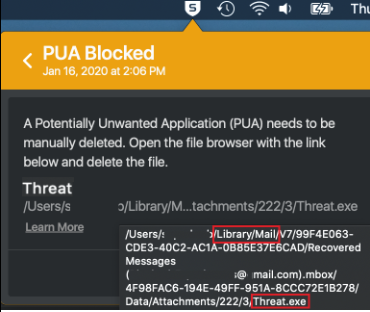
If the file path presented includes /Library/Mail/ then the malware is most likely contained inside an email attachment. Detection example: (Note the location including /Library/Mail, as well as the example threat name at the end)
- Find the location of the detected threat through any of the following options:
- Click on the Manual detection via the Sophos Home Shield and hover the mouse over the threat’s name to see its full path. Click on the path to open it in finder *(please see Note at the bottom if the path doesn’t open in Finder).
OR - Log in to your Sophos Home Dashboard , locate the affected system and use the HISTORY tab to find the detection and its full path , copy the path up until the threat’s name (do not include the threat’s name), then paste it on Spotlight (click on the magnifying glass at the top right –> paste the path and hit Enter to open the location in finder).
Example
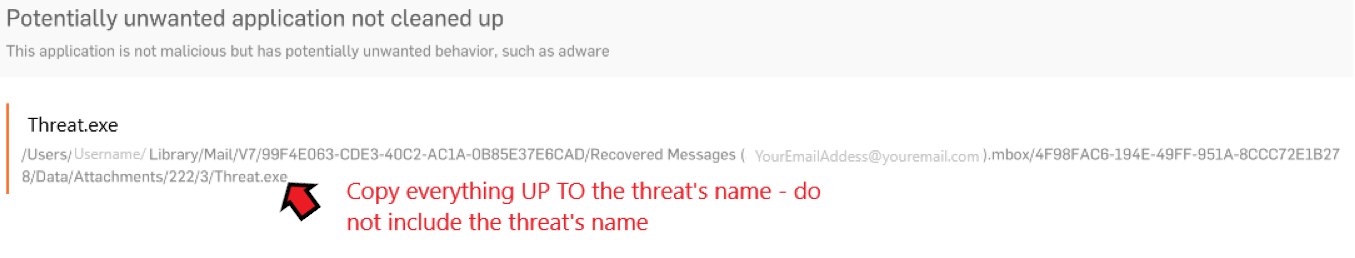
Highlight and copy the path up-to the threat’s name – In this example:
/Users/Username/Library/Mail/V7/99F4E063-CDE3-40C2-AC1A-0B85E37E6CAD/Recovered Messages ([email protected]).mbox/4F98FAC6-194E-49FF-951A-8CCC72E1B278/Data/Attachments/222/3/
Then paste it in Spotlight (click on the Magnifying glass at the top right of your screen)
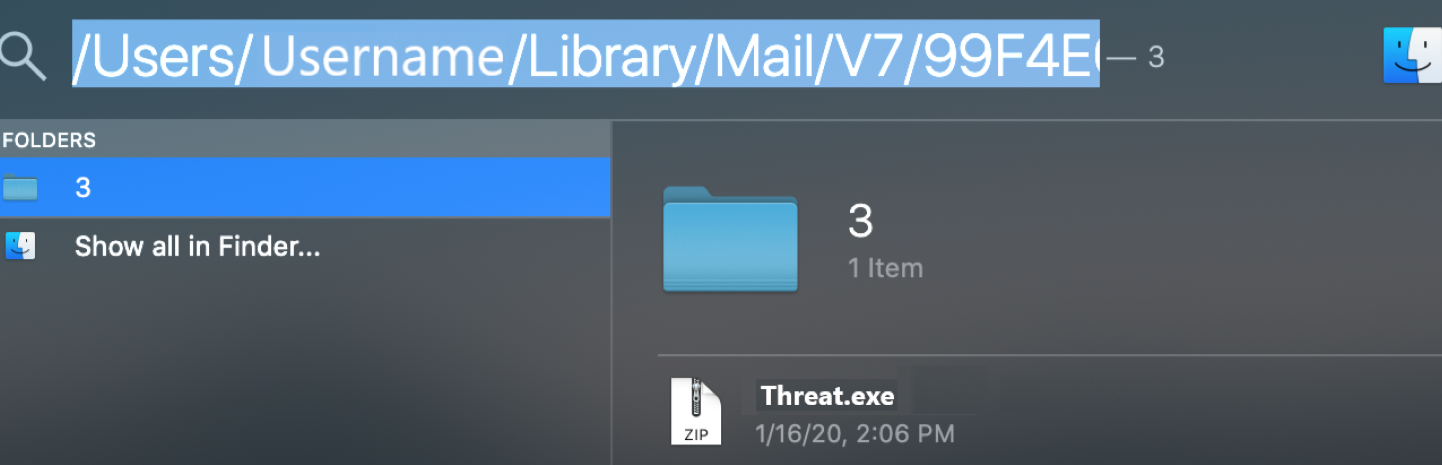
- Click on the Manual detection via the Sophos Home Shield and hover the mouse over the threat’s name to see its full path. Click on the path to open it in finder *(please see Note at the bottom if the path doesn’t open in Finder).
- Delete the file by right-clicking on it –> Move to trash
- Empty the trash
- Open your Mail program, use the search function to search for the threat’s name via “All” your inbox items to locate the email with the offending attachment, then delete it.
- On the Sophos Home Shield find the manual cleanup detection and hit Ignore
- Run a Full System scan
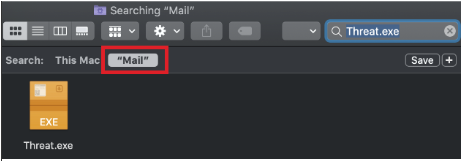
- *Note: To manually browse the Mail folder, click on the magnifying glass at the top of your screen and copy paste the following:
~/Library/Mail - Hit Enter to open the folder
- Use the search bar at the top right to enter the threat’s name, once located, delete it by right-clicking on it –> Move to trash
- Ensure the Search section has “Mail” highlighted, otherwise, it won’t find the threat:
- Empty the trash
Detection is inside a disk image (DMG)
Follow the steps below to manually remove threats detected in a mounted disk image (.dmg file)
- Click on the detection via the Sophos Home Shield
- You will now see the path to where the threat is located. If the file path contains /Volumes/<disk name>, and the <disk name> is not Macintosh HD, Bootcamp or one of your external drives, the malware is in a mounted disk image. In the example below, we can see that the threat is in a mounted disk image volume called “Eicar”
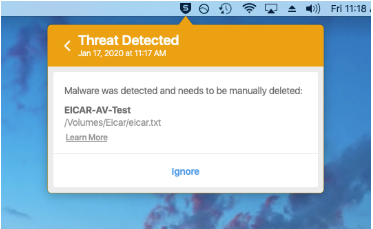
- Go to the Desktop and locate the mounted disk image with the same name as in the path. For example, if the file path contains /Volumes/Eicar, you should see an Eicar disk icon on the desktop.
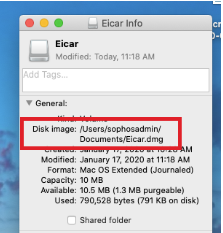
- On the keyboard, press control key and click on the mounted disk > select Get Info. Make note of the file path containing .dmg in the disk image field. See example below:
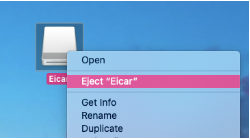
- Press control on the keyboard, then click on the mounted disk icon > select Eject.
- Once the disk is ejected, locate the dmg file identified in Step 4 and delete it.
- Empty the Trash
- On the Sophos Home Shield find the manual cleanup detection and hit Ignore
- Run a Full System scan
Detection is inside Bootcamp backup
If the file path points to /Volumes/BOOTCAMP/, the detection is located in the bootcamp backup.
- Find the location of the detected threat through any of the following options:
- Click on the Manual cleanup detection on the Sophos Home Shield and hover the mouse over the threat’s name to see its full path.
OR - Log in to your Sophos Home Dashboard , locate the affected system and use the HISTORY tab to find the detection and its full path.
- Click on the Manual cleanup detection on the Sophos Home Shield and hover the mouse over the threat’s name to see its full path.
- Make a note of the full path where the threat is detected.
- Reboot the Mac into Windows.
- Using Windows Explorer, browse to the location of the threat and delete it manually. (If Sophos Home installed on the Windows operating system, run a full scan after the cleanup).
- Reboot back to MacOS and run a Full System scan .
Detection is in a temporary Folder Locations
The folders /tmp, /private, /var are temporary folders and should be automatically emptied upon restart. If you see a detection in one of these folders which requires a manual cleanup, restart the Mac and run another Full System Scan to ensure the threat is now gone.

