Begin your ASR rules deployment with ring 1.
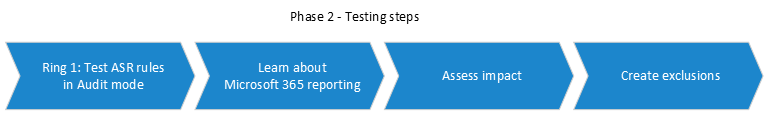
Step 1: Test ASR rules using Audit
Begin the testing phase by turning on the ASR rules with the rules set to Audit, starting with your champion users or devices in ring 1. Typically, the recommendation is that you enable all the rules (in Audit) so that you can determine which rules are triggered during the testing phase. Note that rules that are set to Audit do not generally impact functionality of the entity or entities to which the rule is applied but do generate logged events for the evaluation; there is no effect on end users.
Configure ASR Rules using MEM
You can use Microsoft Endpoint Manager (MEM) Endpoint Security to configure custom ASR rules.
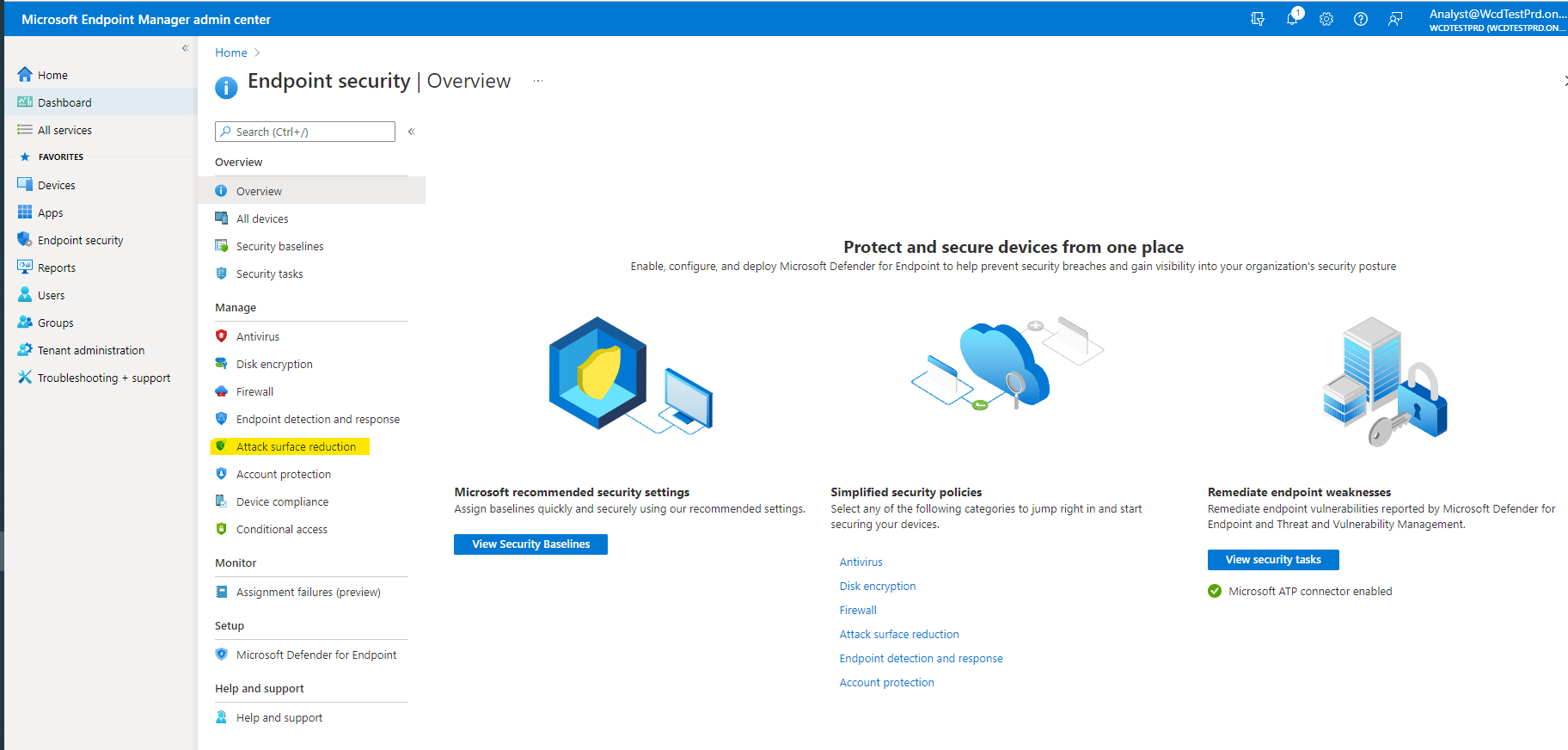
- Open Microsoft Endpoint Manager admin center
- Go to Endpoint Security > Attack surface reduction.
- Select Create Policy.
- In Platform, select Windows 10 and later, and in Profile, select Attack surface reduction rules.
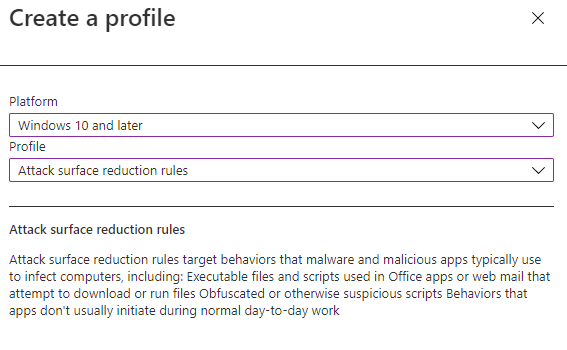
- Click Create.
- In the Basics tab of the Create profile pane, in Name add a name for your policy. In Description add a description for your ASR rules policy.
- In the Configuration settings tab, under Attack Surface Reduction Rules, set all rules to Audit mode.
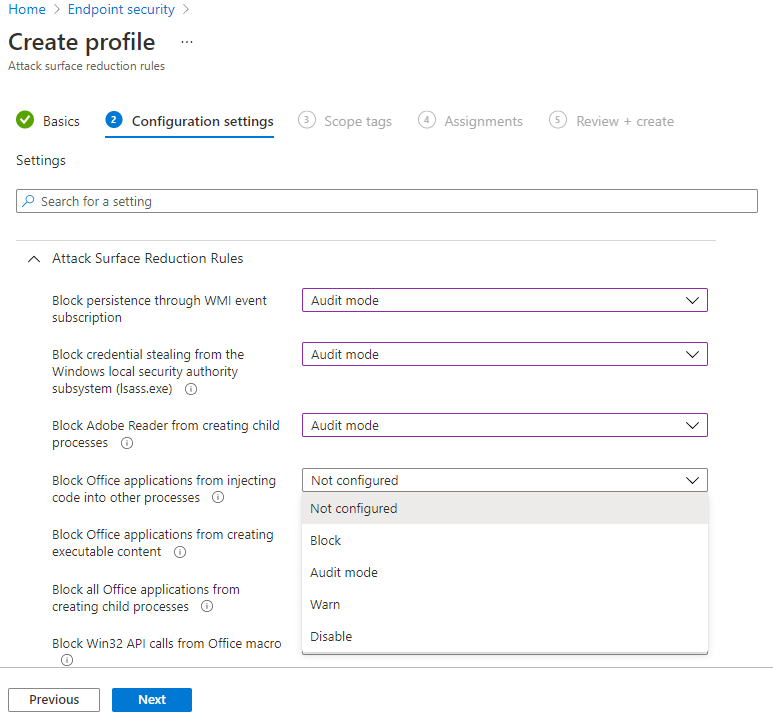
Note
There are variations in some ASR rules mode listings; Blocked and Enabled provide the same functionality.
- [Optional] In the Scope tags pane, you can add tag information to specific devices. You can also use role-based access control and scope tags to make sure that the right admins have the right access and visibility to the right Intune objects. Learn more: Use role-based access control (RBAC) and scope tags for distributed IT in Intune.
- In the Assignments pane, you can deploy or “assign” the profile to your user or device groups. Learn more: Assign device profiles in Microsoft Intune
- Review your settings in the Review + create pane. Click Create to apply the rules.
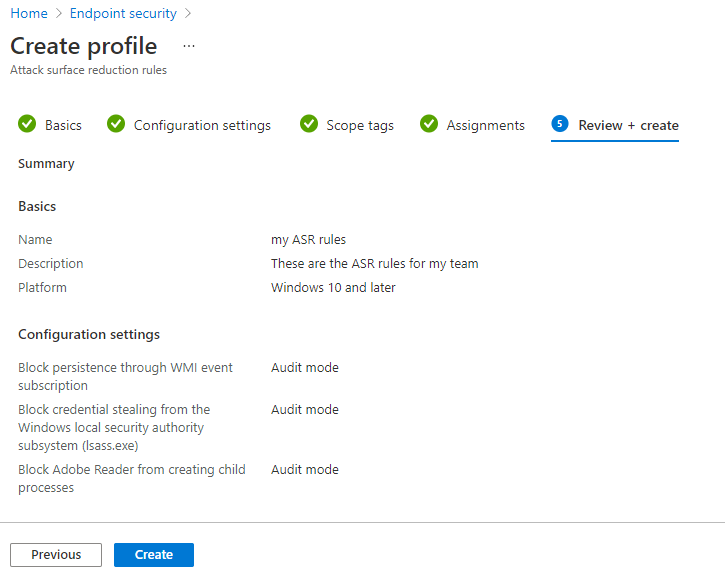
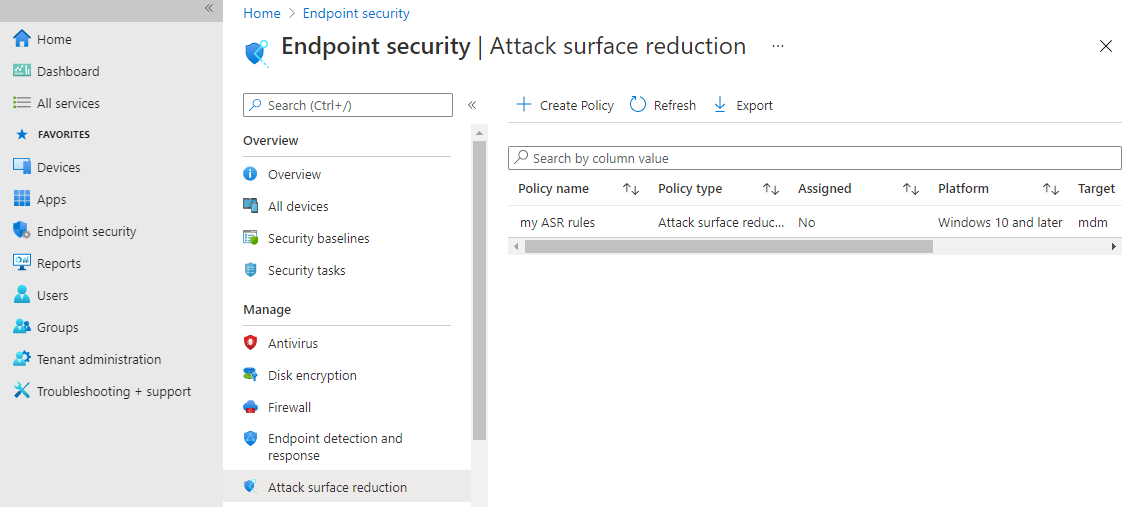
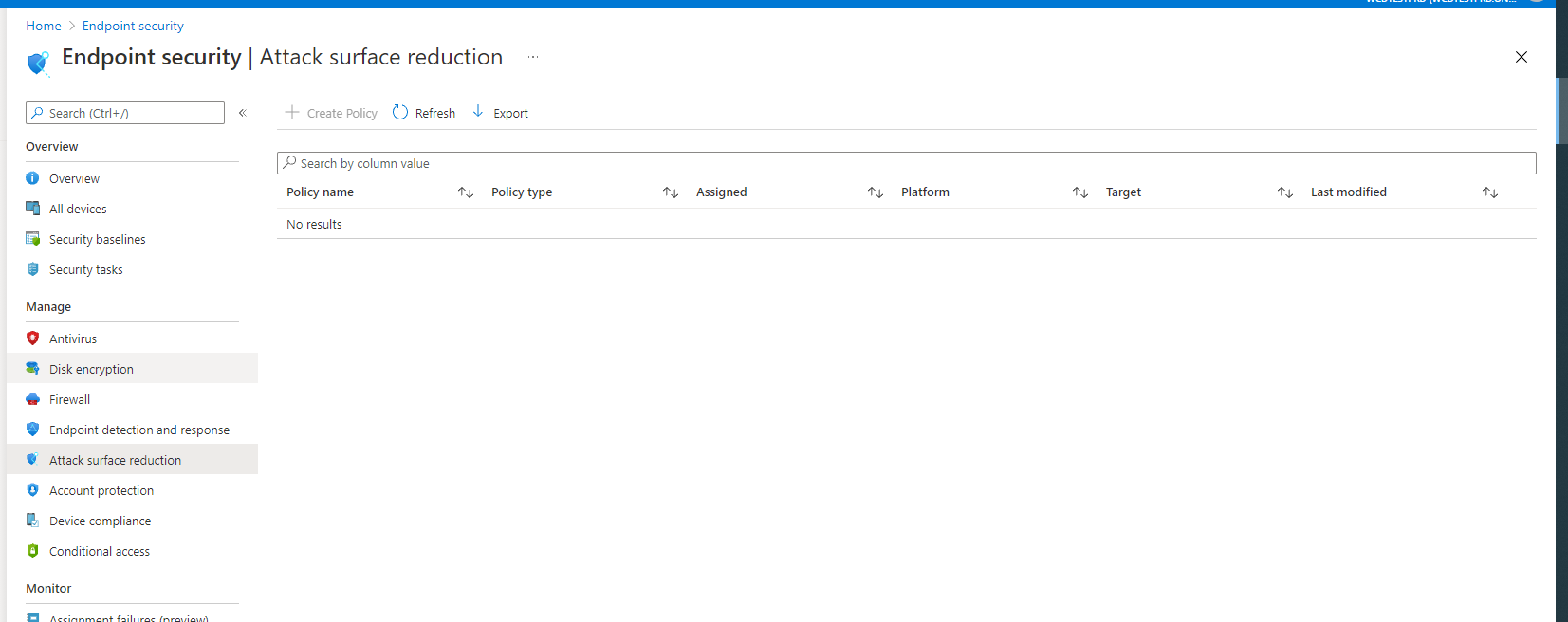
Your new attack surface reduction policy for ASR rules is listed in Endpoint security | Attack surface reduction.
Step 2: Understand the Attack surface reduction rules reporting page in the Microsoft 365 Defender portal
The ASR rules reporting page is found in Microsoft 365 Defender portal > Reports > Attack surface reduction rules. This page has three tabs:
- Detections
- Configuration
- Add exclusions
Detections tab
Provides a 30-day timeline of detected audit and blocked events.
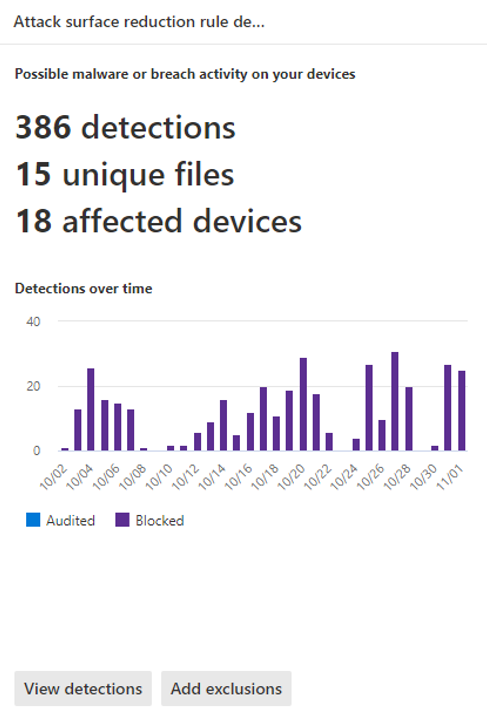
The Attack Surface reduction rules pane provides an overview of detected events on a per-rule basis.
Note
There are some variations in ASR rules reports. Microsoft is in the process of updating the behavior of the ASR rules reports to provide a consistent experience.

Click View detections to open the Detections tab.
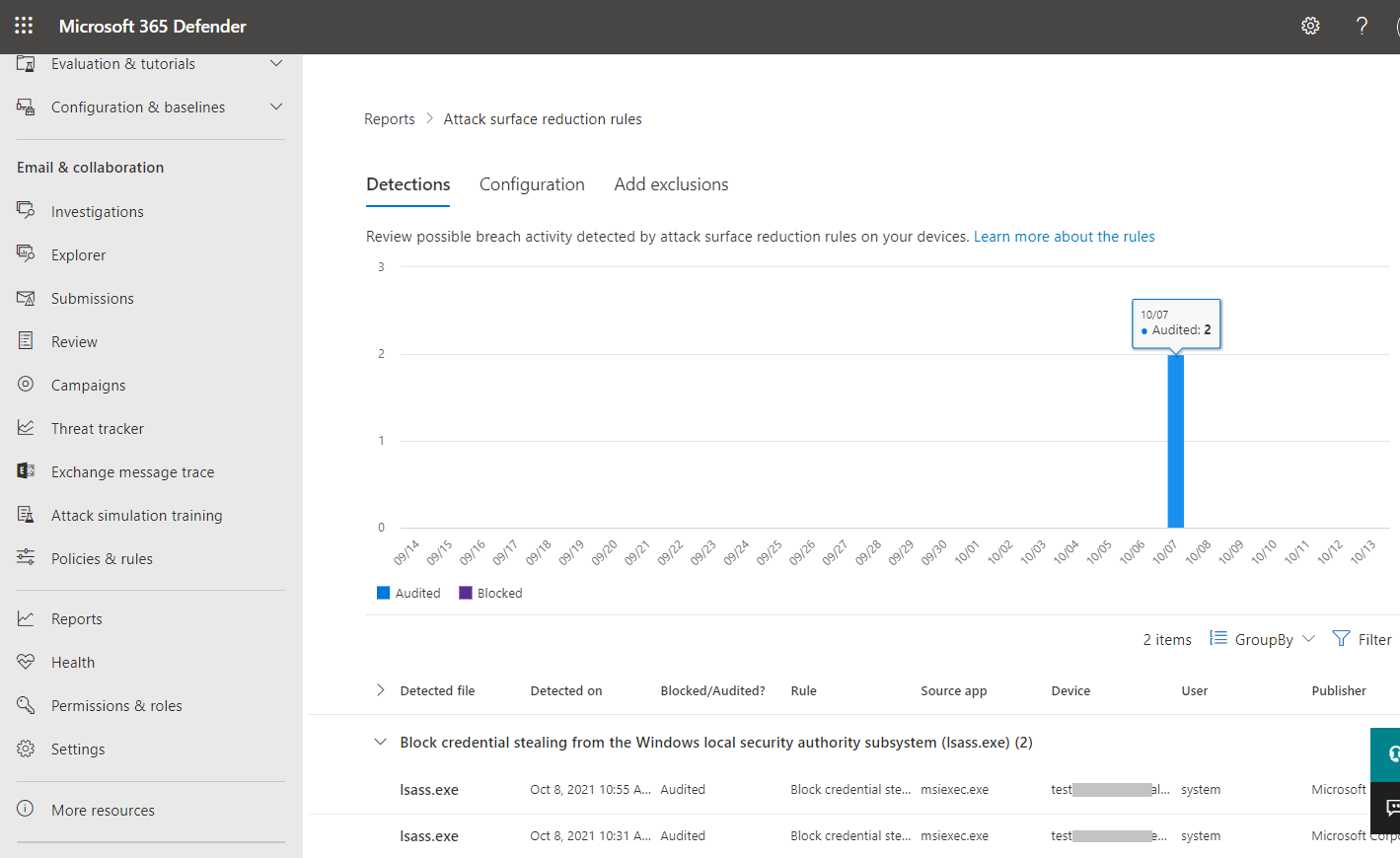
The GroupBy and Filter pane provide the following options:
The GroupBy returns results set to the following groups:
- No grouping
- Detected file
- Audit or block
- Rule
- Source app
- Device
- User
- Publisher
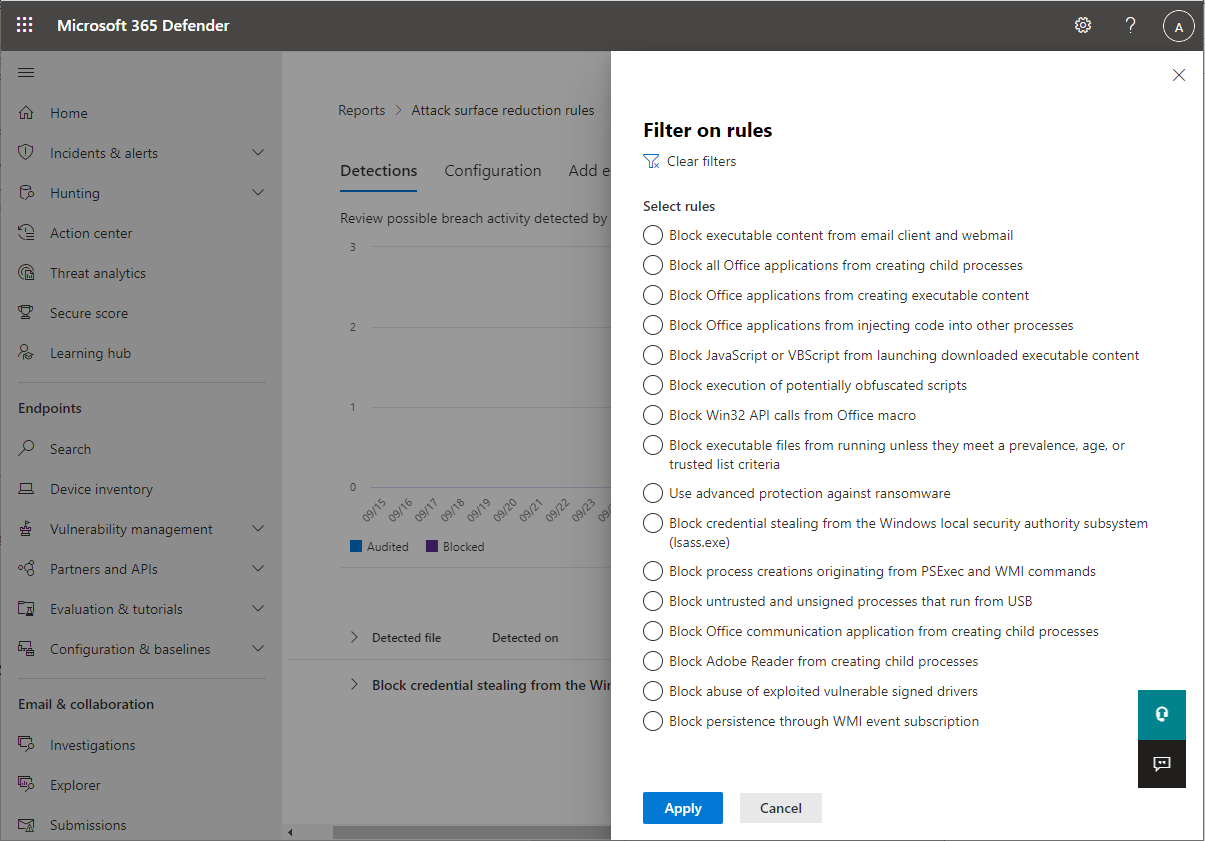
Filter opens the Filter on rules page, which enables you to scope the results to only the selected ASR rules:
Note
If you have a Microsoft Microsoft 365 Security E5 or A5, Windows E5 or A5 license, the following link opens the Microsoft Defender 365 Reports > Attack surface reductions > Detections tab.
Configuration tab
Lists – on a per-computer basis – the aggregate state of ASR rules: Off, Audit, Block.
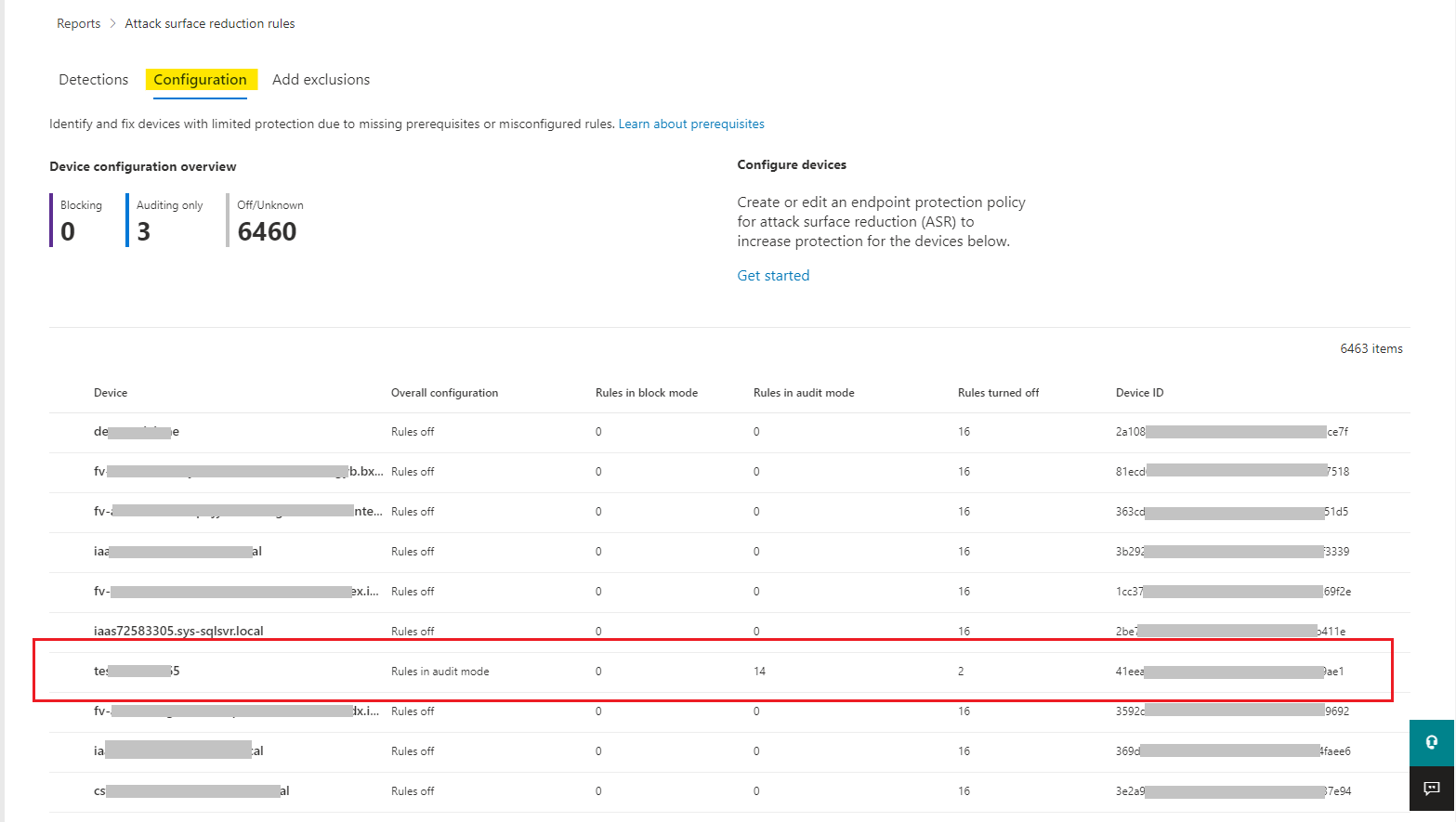
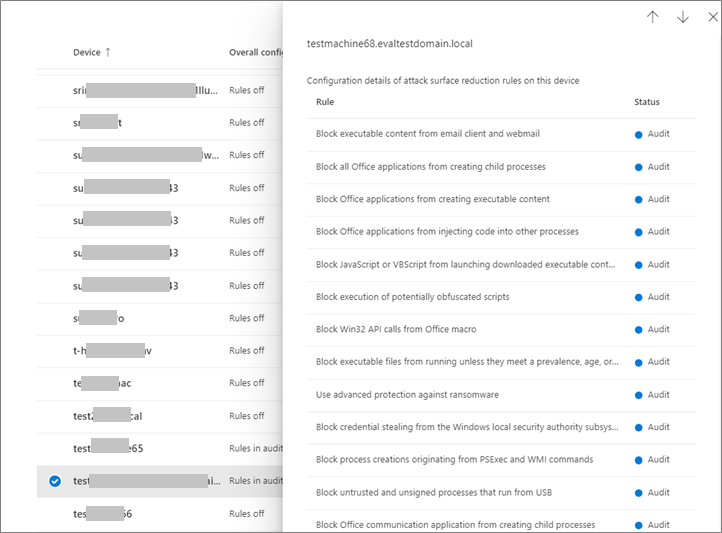
On the Configurations tab, you can check – on a per-device basis – which ASR rules are enabled, and in which mode, by selecting the device for which you want to review ASR rules.
The Get started link opens the Microsoft Endpoint Manager admin center, where you can create or modify an endpoint protection policy for ASR:
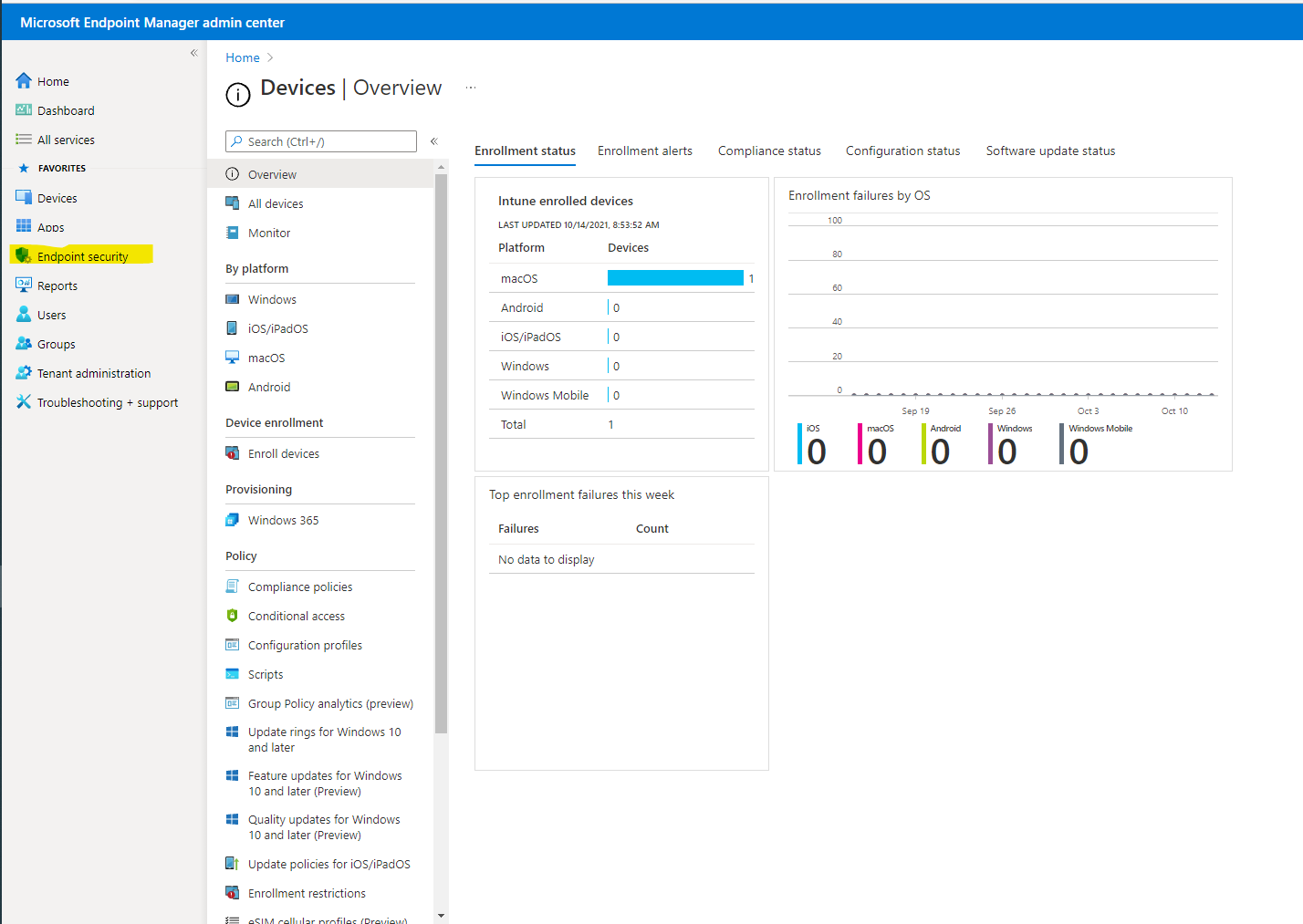
In Endpoint security | Overview, select Attack surface reduction:
The Endpoint Security | Attack surface reduction pane opens:
Note
If you have a Microsoft Defender 365 E5 (or Windows E5?) license, this link will open the Microsoft Defender 365 Reports > Attack surface reductions > Configurations tab.
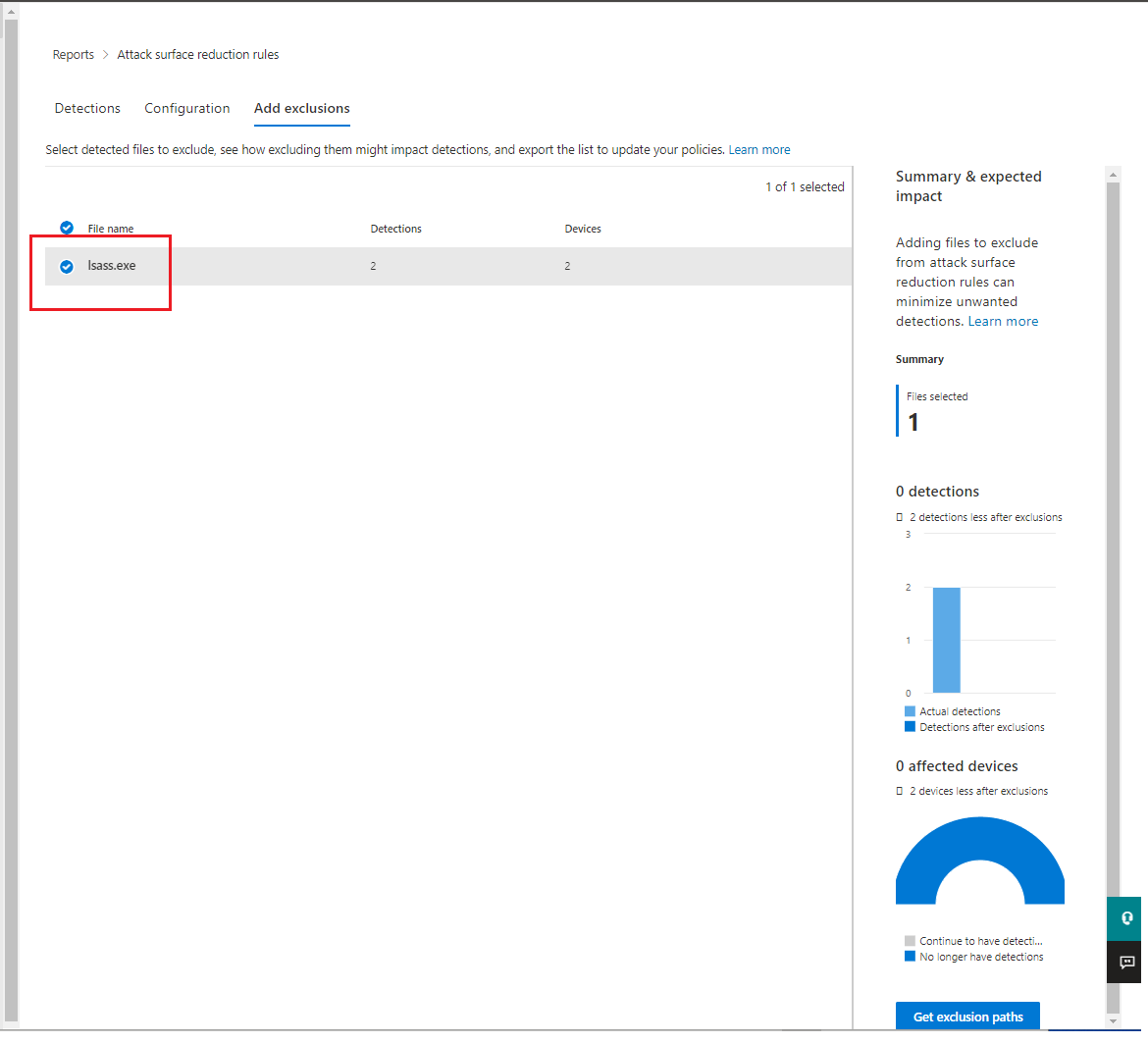
Add exclusions
This tab provides a method to select detected entities (for example, false positives) for exclusion. When exclusions are added, the report provides a summary of the expected impact.
Note
Microsoft Defender Antivirus AV exclusions are honored by ASR rules. See Configure and validate exclusions based on extension, name, or location.
Note
If you have a Microsoft Defender 365 E5 (or Windows E5?) license, this link will open the Microsoft Defender 365 Reports > Attack surface reductions > Exclusions tab.
Use PowerShell as an alternative method to enable ASR rules
You can use PowerShell – as an alternative to MEM – to enable ASR rules in audit mode to view a record of apps that would have been blocked if the feature was fully enabled. You can also get an idea of how often the rules will fire during normal use.
To enable an attack surface reduction rule in audit mode, use the following PowerShell cmdlet:
Add-MpPreference -AttackSurfaceReductionRules_Ids <rule ID> -AttackSurfaceReductionRules_Actions AuditMode
Where <rule ID> is a GUID value of the attack surface reduction rule.
To enable all the added attack surface reduction rules in audit mode, use the following PowerShell cmdlet:
(Get-MpPreference).AttackSurfaceReductionRules_Ids | Foreach {Add-MpPreference -AttackSurfaceReductionRules_Ids $_ -AttackSurfaceReductionRules_Actions AuditMode}
Tip
If you want to fully audit how attack surface reduction rules will work in your organization, you’ll need to use a management tool to deploy this setting to devices in your network(s).
You can also use Group Policy, Intune, or mobile device management (MDM) configuration service providers (CSPs) to configure and deploy the setting. Learn more in the main Attack surface reduction rules article.
Use Windows Event Viewer Review as an alternative to the attack surface reduction rules reporting page in the Microsoft 365 Defender portal
To review apps that would have been blocked, open Event Viewer and filter for Event ID 1121 in the Microsoft-Windows-Windows Defender/Operational log. The following table lists all network protection events.
| Event ID | Description |
|---|---|
| 5007 | Event when settings are changed |
| 1121 | Event when an attack surface reduction rule fires in block mode |
| 1122 | Event when an attack surface reduction rule fires in audit mode |

