Automating security procedures is a standard requirement for every modern Security Operations Center. The lack of professional cyber defenders forces SOC to work in the most efficient way and automation is a must. Microsoft Power Automate supports different connectors that were built exactly for that. You can build an end-to-end procedure automation within a few minutes.
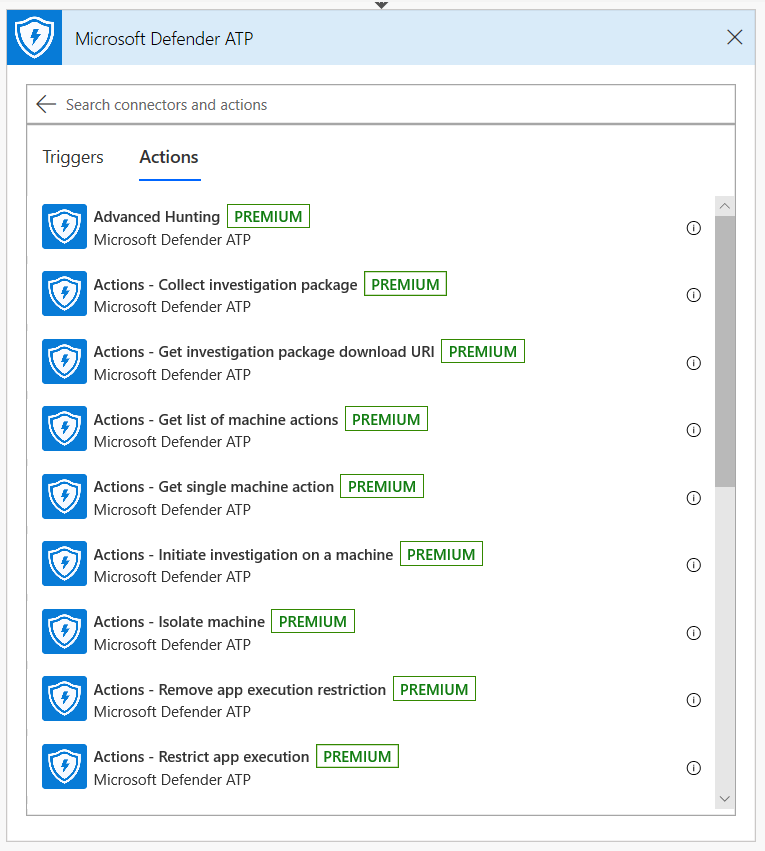
Microsoft Defender API has an official Power Automate Connector with many capabilities.
Note
For more details about premium connectors licensing prerequisites, see Licensing for premium connectors.
Usage example
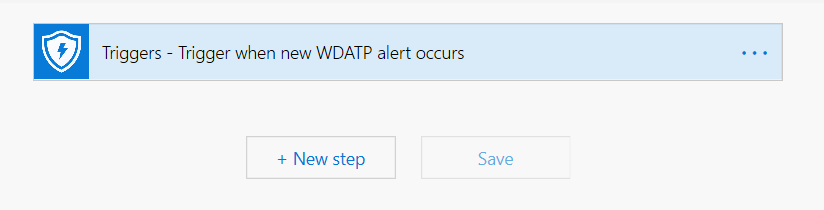
The following example demonstrates how to create a Flow that is triggered any time a new Alert occurs on your tenant.
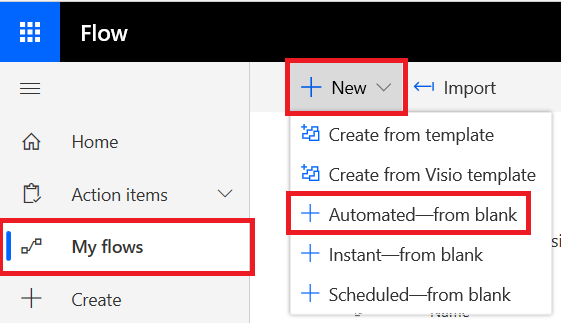
- Log in to Microsoft Power Automate.
- Go to My flows > New > Automated-from blank.
- Choose a name for your Flow, search for “Microsoft Defender ATP Triggers” as the trigger, and then select the new Alerts trigger.
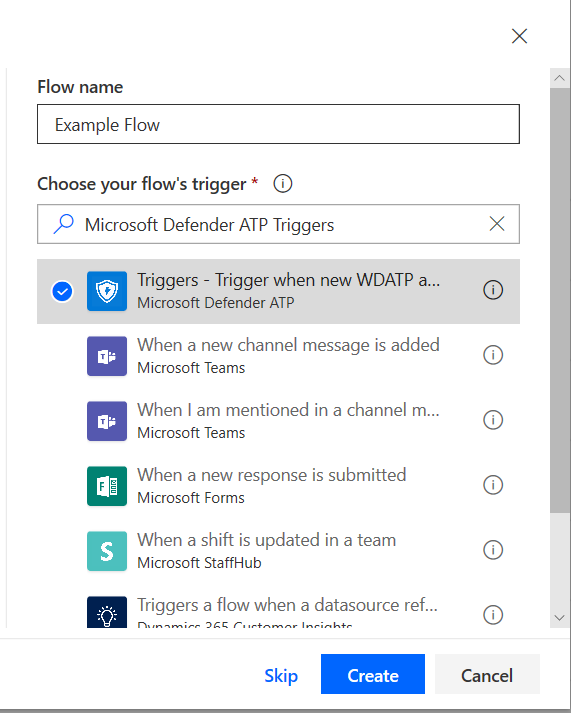
Now you have a Flow that is triggered every time a new Alert occurs.
All you need to do now is choose your next steps. For example, you can isolate the device if the Severity of the Alert is High and send an email about it. The Alert trigger provides only the Alert ID and the Machine ID. You can use the connector to expand these entities.
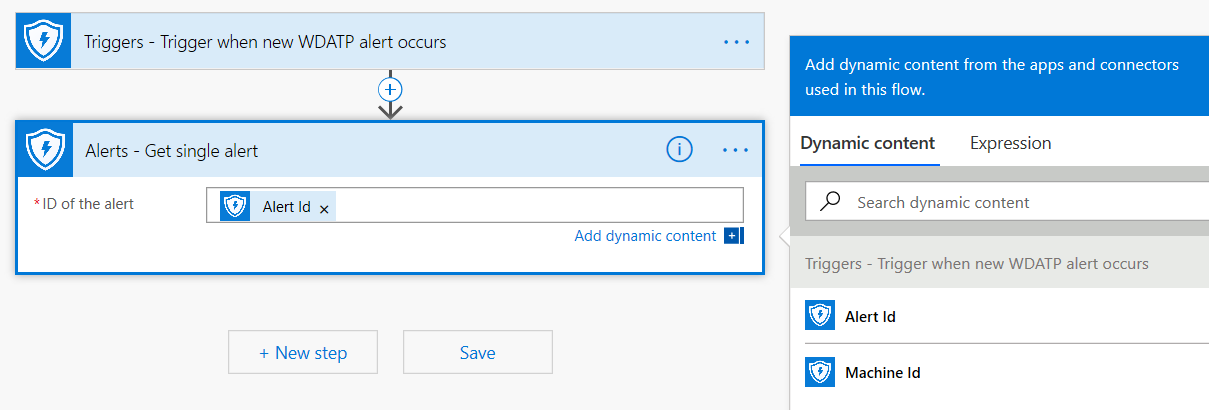
Get the Alert entity using the connector
- Choose Microsoft Defender ATP for the new step.
- Choose Alerts – Get single alert API.
- Set the Alert ID from the last step as Input.
Isolate the device if the Alert’s severity is High
- Add Condition as a new step.
- Check if the Alert severity is equal to High.
If yes, add the Microsoft Defender ATP – Isolate machine action with the Machine ID and a comment.
- Add a new step for emailing about the Alert and the Isolation. There are multiple email connectors that are very easy to use, such as Outlook or Gmail.
- Save your flow.
You can also create a scheduled flow that runs Advanced Hunting queries and much more!