This topic describes how to deploy Microsoft Defender for Endpoint on macOS manually. A successful deployment requires the completion of all of the following steps:
- Download installation and onboarding packages
- Application installation (macOS 10.15 and older versions)
- Application installation (macOS 11 and newer versions)
- Client configuration
Prerequisites and system requirements
Before you get started, see the main Microsoft Defender for Endpoint on macOS page for a description of prerequisites and system requirements for the current software version.
Download installation and onboarding packages
Download the installation and onboarding packages from Microsoft 365 Defender portal:
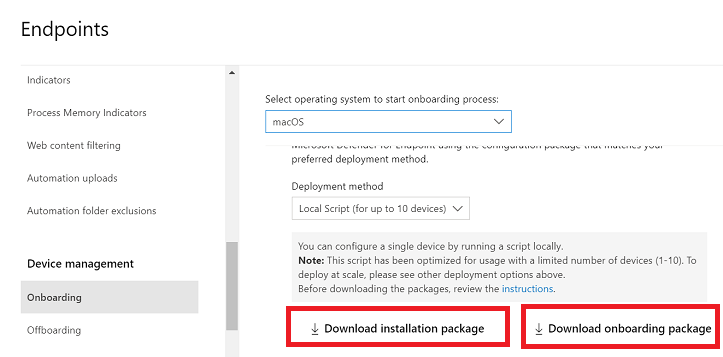
- In Microsoft 365 Defender portal, go to Settings > Endpoints > Device management > Onboarding.
- In Section 1 of the page, set operating system to macOS and Deployment method to Local script.
- In Section 2 of the page, select Download installation package. Save it as wdav.pkg to a local directory.
- In Section 2 of the page, select Download onboarding package. Save it as WindowsDefenderATPOnboardingPackage.zip to the same directory.
- From a command prompt, verify that you have the two files.
Application installation (macOS 10.15 and older versions)
To complete this process, you must have admin privileges on the device.
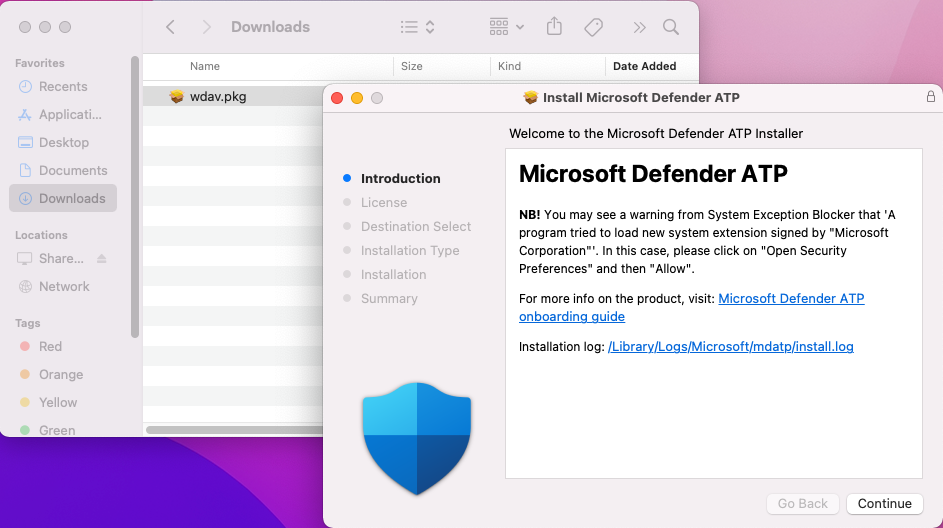
- Navigate to the downloaded wdav.pkg in Finder and open it.
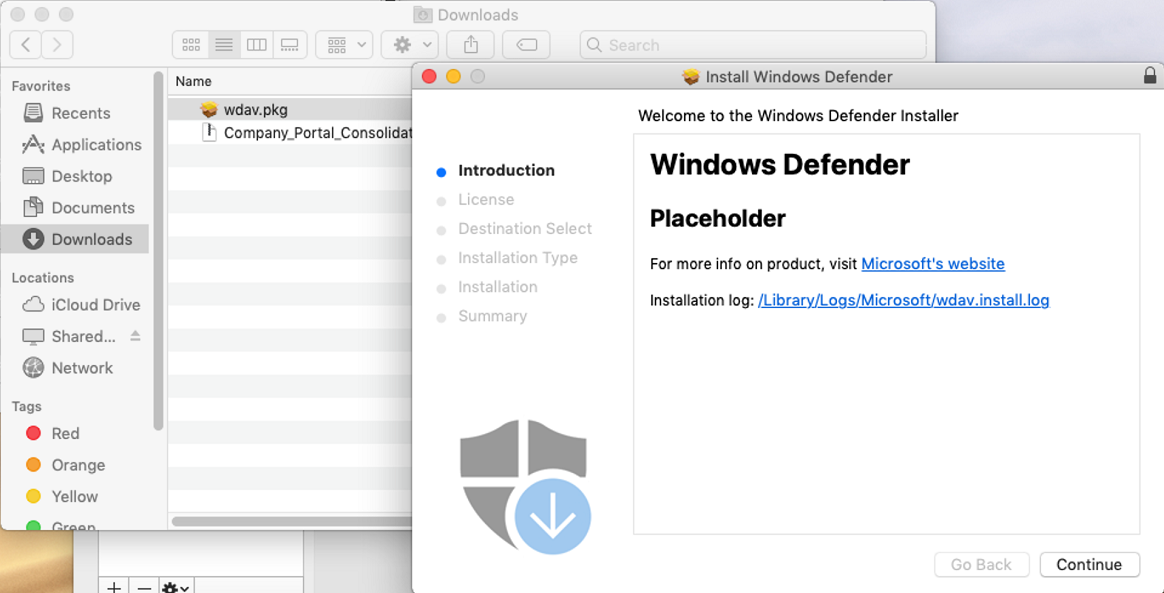
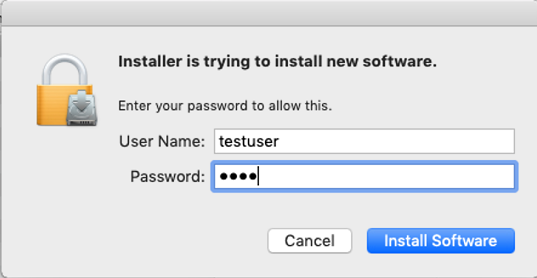
- Select Continue, agree with the License terms, and enter the password when prompted.
Important
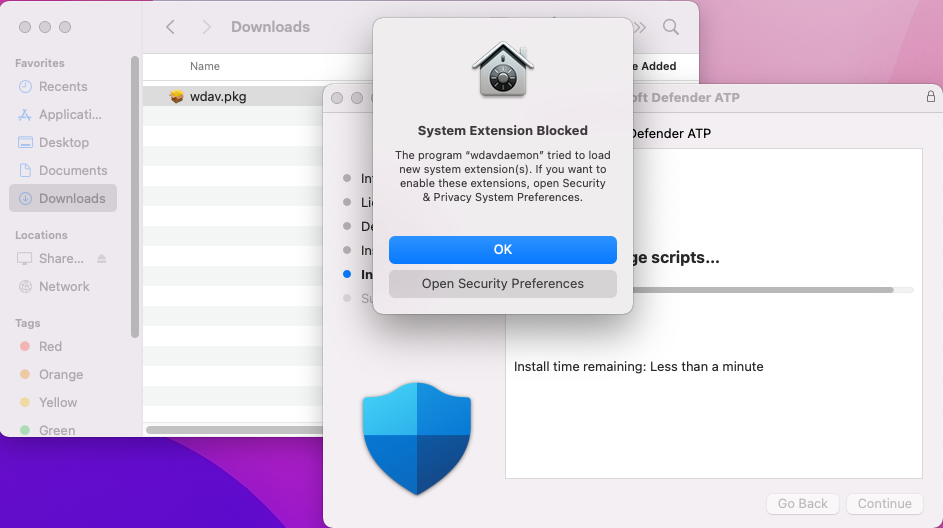
You will be prompted to allow a driver from Microsoft to be installed (either “System Extension Blocked” or “Installation is on hold” or both. The driver must be allowed to be installed.
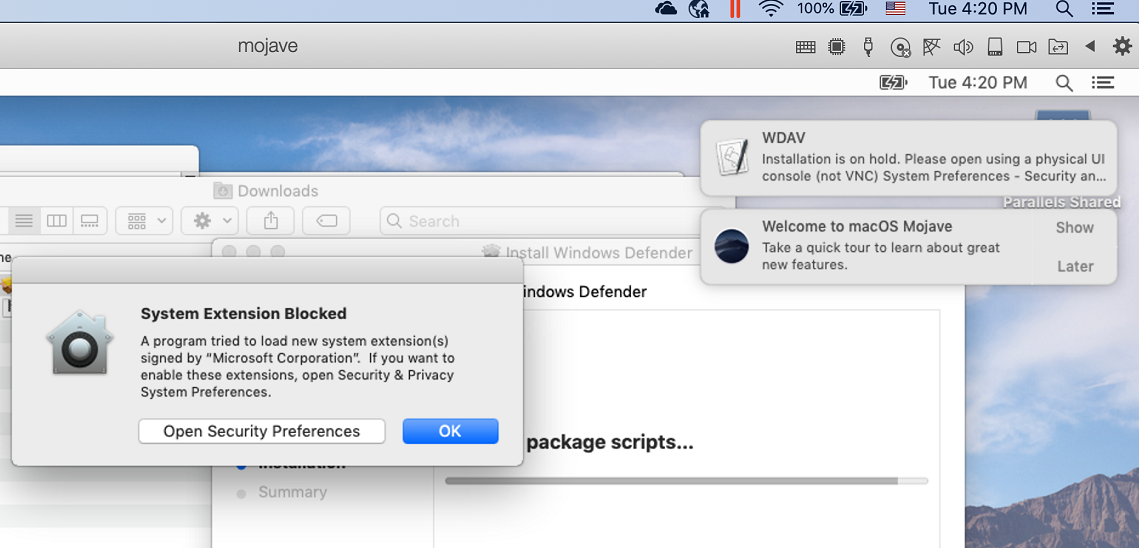
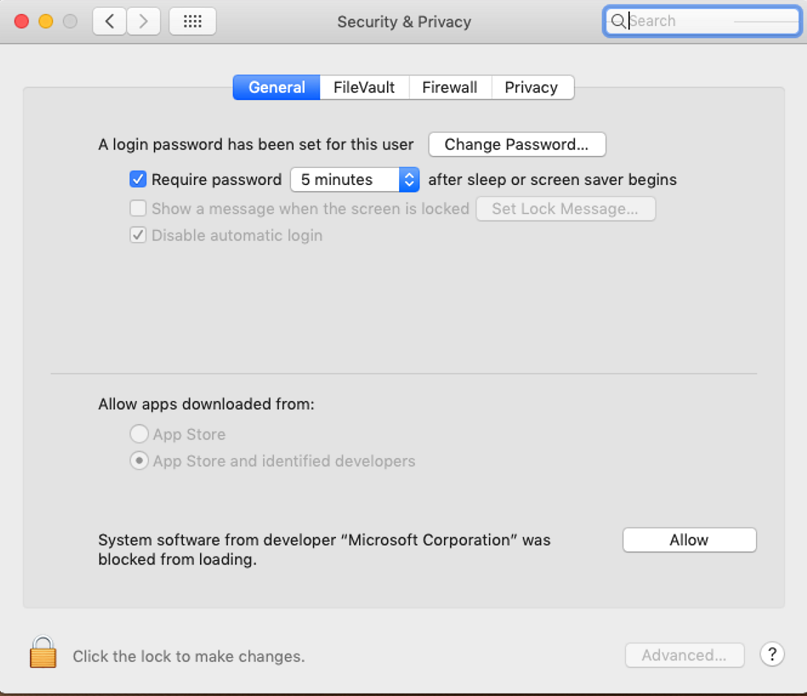
- Select Open Security Preferences or Open System Preferences > Security & Privacy. Select Allow:
The installation proceeds.
Caution
If you don’t select Allow, the installation will proceed after 5 minutes. Microsoft Defender for Endpoint will be loaded, but some features, such as real-time protection, will be disabled. See Troubleshoot kernel extension issues for information on how to resolve this.
Note
macOS may request to reboot the device upon the first installation of Microsoft Defender for Endpoint. Real-time protection will not be available until the device is rebooted.
Application installation (macOS 11 and newer versions)
To complete this process, you must have admin privileges on the device.
- Navigate to the downloaded wdav.pkg in Finder and open it.
- Select Continue, agree with the License terms, and enter the password when prompted.
- At the end of the installation process, you’ll be promoted to approve the system extensions used by the product. Select Open Security Preferences.
- From the Security & Privacy window, select Allow.
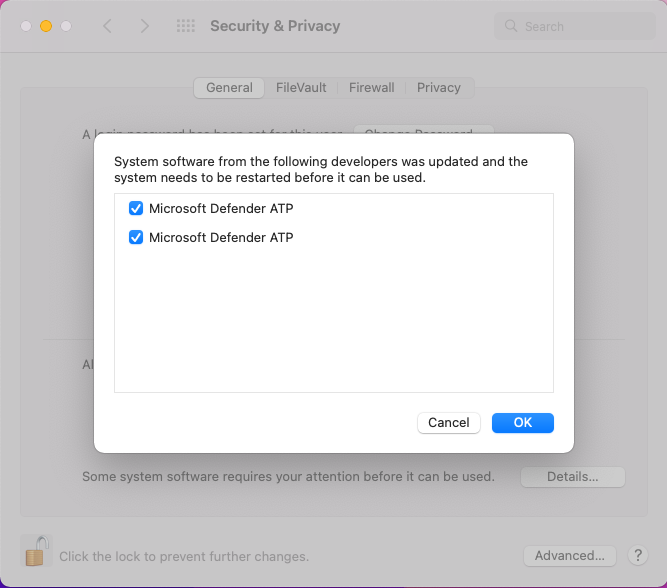
- Repeat steps 3 & 4 for all system extensions distributed with Microsoft Defender for Endpoint on Mac.
- As part of the Endpoint Detection and Response capabilities, Microsoft Defender for Endpoint on Mac inspects socket traffic and reports this information to the Microsoft 365 Defender portal. When prompted to grant Microsoft Defender for Endpoint permissions to filter network traffic, select Allow.

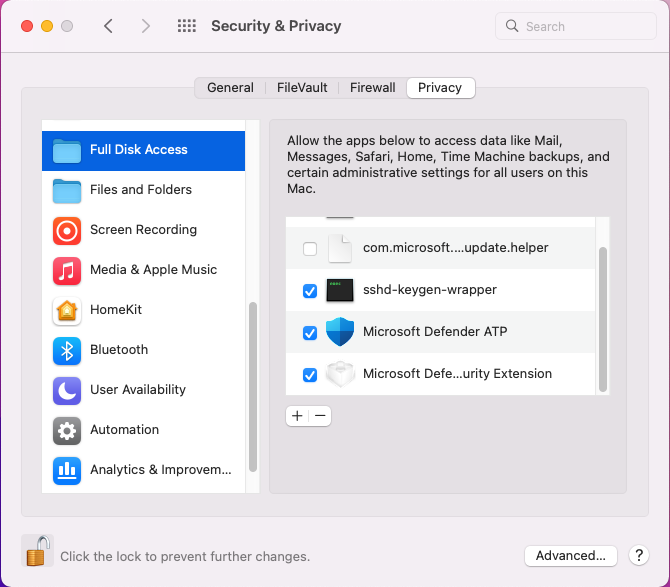
- Open System Preferences > Security & Privacy and navigate to the Privacy tab. Grant Full Disk Access permission to Microsoft Defender ATP and Microsoft Defender ATP Endpoint Security Extension.
Client configuration
- Copy wdav.pkg and MicrosoftDefenderATPOnboardingMacOs.py to the device where you deploy Microsoft Defender for Endpoint on macOS.
The client device isn’t associated with org_id. Note that the org_id attribute is blank.
Bashmdatp health --field org_id - Run the Python script to install the configuration file:
Bash
/usr/bin/python MicrosoftDefenderATPOnboardingMacOs.py - Verify that the device is now associated with your organization and reports a valid org ID:
Bash
mdatp health --field org_idAfter installation, you’ll see the Microsoft Defender icon in the macOS status bar in the top-right corner.
How to Allow Full Disk Access
Caution
macOS 10.15 (Catalina) contains new security and privacy enhancements. Beginning with this version, by default, applications are not able to access certain locations on disk (such as Documents, Downloads, Desktop, etc.) without explicit consent. In the absence of this consent, Microsoft Defender for Endpoint is not able to fully protect your device.
- To grant consent, open System Preferences > Security & Privacy > Privacy > Full Disk Access. Click the lock icon to make changes (bottom of the dialog box). Select Microsoft Defender for Endpoint.
- Run an AV detection test to verify that the device is properly onboarded and reporting to the service. Perform the following steps on the newly onboarded device:
- Ensure that real-time protection is enabled (denoted by a result of 1 from running the following command):
Bash
mdatp health --field real_time_protection_enabled - Open a Terminal window. Copy and execute the following command:
Bash
curl -o ~/Downloads/eicar.com.txt https://www.eicar.org/download/eicar.com.txt - The file should have been quarantined by Defender for Endpoint on Mac. Use the following command to list all the detected threats:
Bash
mdatp threat list
- Ensure that real-time protection is enabled (denoted by a result of 1 from running the following command):
- Run an EDR detection test to verify that the device is properly onboarded and reporting to the service. Perform the following steps on the newly onboarded device:
- In your browser such as Microsoft Edge for Mac or Safari.
- Download MDATP MacOS DIY.zip from https://aka.ms/mdatpmacosdiy and extract.
You may be prompted:
Do you want to allow downloads on “mdatpclientanalyzer.blob.core.windows.net”?
You can change which websites can download files in Websites Preferences.
- Click Allow.
- Open Downloads.
- You should see MDATP MacOS DIY.
Tip
If you double-click, you will get the following message:
“MDATP MacOS DIY” cannot be opened because the developer cannot be verifier.
macOS cannot verify that this app is free from malware.
[Move to Trash] [Cancel] - Click Cancel.
- Right-click MDATP MacOS DIY, and then click Open.
The system should display the following message:
macOS cannot verify the developer of MDATP MacOS DIY. Are you sure you want to open it?
By opening this app, you will be overriding system security which can expose your computer and personal information to malware that may harm your Mac or compromise your privacy. - Click Open.
The system should display the following message:
Microsoft Defender for Endpoint – macOS EDR DIY test file
Corresponding alert will be available in the MDATP portal. - Click Open.
In a few minutes an alert named “macOS EDR Test Alert” should be raised.
- Go to Microsoft 365 Defender portal (https://security.microsoft.com/).
- Go to the Alert Queue.
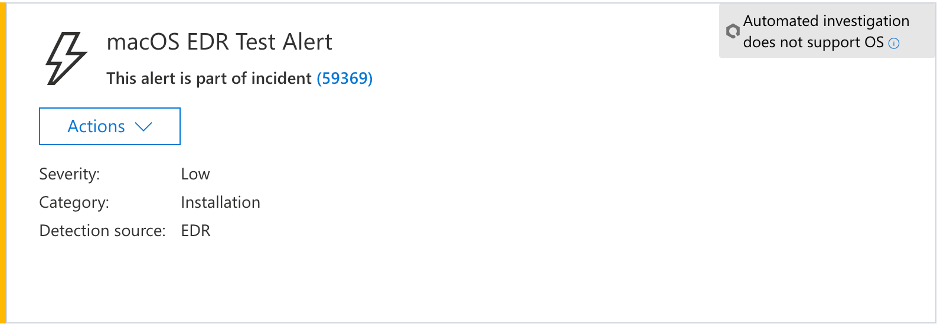
Look at the alert details and the device timeline, and perform the regular investigation steps.
Logging installation issues
See Logging installation issues for more information on how to find the automatically generated log that is created by the installer when an error occurs.
Uninstallation
See Uninstalling for details on how to remove Microsoft Defender for Endpoint on macOS from client devices.

