Note
We’ve renamed Microsoft Cloud App Security. It’s now called Microsoft Defender for Cloud Apps. In the coming weeks, we’ll update the screenshots and instructions here and in related pages. For more information about the change, see this announcement. To learn more about the recent renaming of Microsoft security services, see the Microsoft Ignite Security blog.
If you work with both Defender for Cloud Apps and Corrata, you can integrate the two products to enhance your security Cloud Discovery experience for mobile app use. Corrata, as a local Mobile gateway, monitors your organization’s traffic from mobile devices enabling you to set policies for blocking transactions. Together, Defender for Cloud Apps and Corrata provide the following capabilities:
- Seamless deployment of Cloud Discovery – Use Corrata to collect your mobile device traffic and send it to Defender for Cloud Apps. This eliminates the need for installation of log collectors on your network endpoints to enable Cloud Discovery.
- Corrata’s block capabilities are automatically applied on apps you set as unsanctioned in Defender for Cloud Apps.
- Enhance your Corrata portal with the Defender for Cloud Apps risk assessment for leading cloud apps, which can be viewed directly in the Corrata portal.
Prerequisites
- A valid license for Microsoft Defender for Cloud Apps
- A valid license for Corrata Cloud
Deployment
- In the Corrata portal, do the steps to complete the Corrata partner integration with Microsoft Defender for Cloud Apps.
- In the Defender for Cloud Apps portal, do the following integration steps:
- Click on the settings cog and select Cloud Discovery Settings.
- Click on the Automatic log upload tab and then click Add data source.
- In the Add data source page, enter the following settings:
- Name = Corrata
- Source = Corrata
- Receiver type = FTP
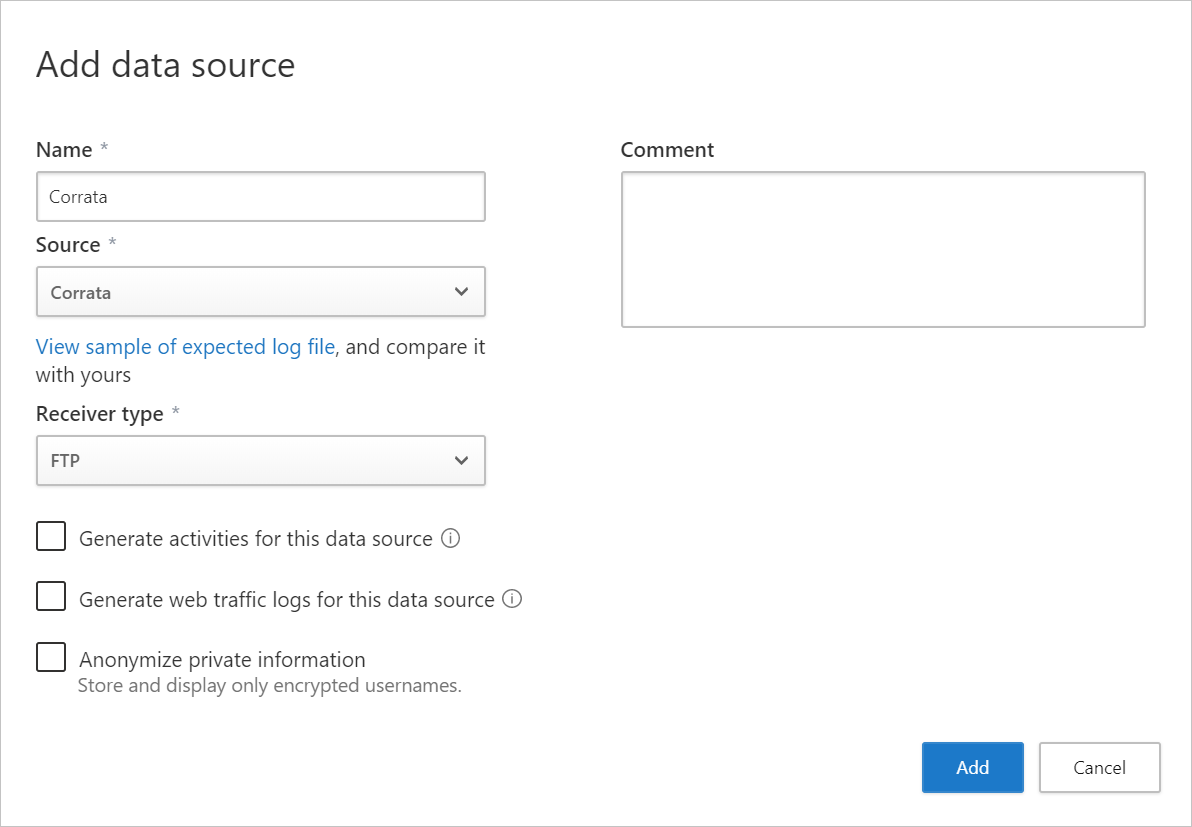
- Click View sample of expected log file. Then click Download sample log to view a sample discovery log, and make sure it matches your logs.
- Investigate cloud apps discovered on your network. For more information and investigation steps, see Working with Cloud Discovery.
- Any app that you set as unsanctioned in Defender for Cloud Apps will be pinged by Corrata, and then automatically blocked by Corrata. For more information about unsanctioning apps, see Sanctioning/unsanctioning an app.

