App governance collects threat alerts that are generated by built-in, machine-learning-driven app governance detection methods based on malicious app activities and policy-based alerts generated by active app policies that you create.
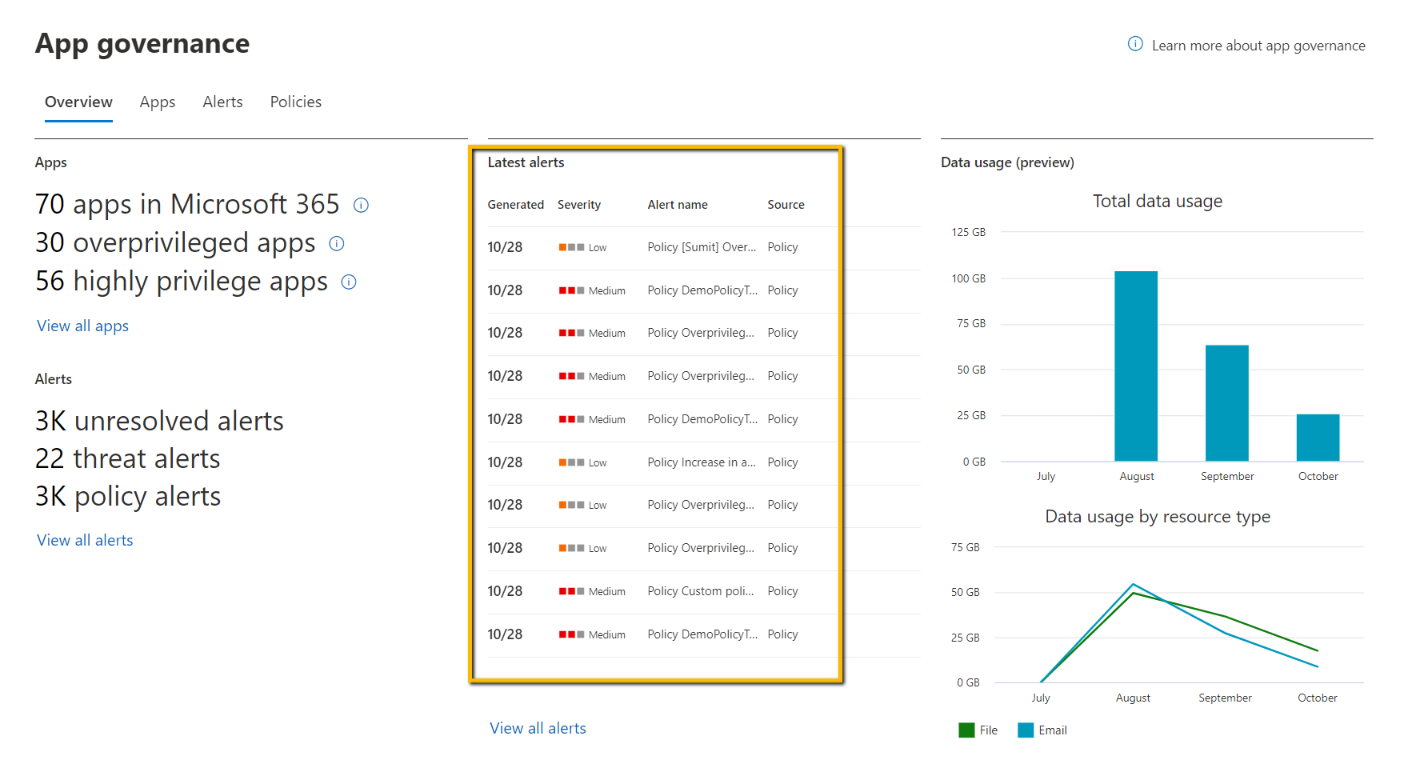
The first place to view app alerts is the app governance dashboard at https://aka.ms/appgovernance.
On this overview page, the Latest alerts section lists the most recent alerts. You can use this to quickly see the current app alert activity for your tenant.
To see all of the alerts, select the Alerts tab.
What’s available on the Alerts page
The Alerts page lists all of the app governance-based alerts for your tenant.
Each listed alert has the following information:
- Alert name: The type of anomalous behavior.
- App name: The app that generated the alert.
- Severity: The severity assigned by app governance for alerts it creates or the severity of the app policy that generated the alert.
- Source: Origination of the alert, which can be results from policy (user-created policies), detection (built-in detection policies), or Defender for Cloud Apps.
- Status: New indicates an alert that hasn’t been assigned a status. Once assigned, the status is either In progress while being investigated or Resolved for alerts that have been addressed through automatic or manual remediation.
- Date created: The date the alert was generated by either app governance detection or through an app policy. All dates shown are in the local time zone of the Microsoft 365 Defender.
- Last activity: The date the status of the alert was last changed. All dates shown are in the local time zone of the Microsoft 365 Defender.
The alert list is sorted by Date created by default. To sort the list by another attribute, select the attribute name.
You can also export the current alert list to a comma-separated value (CSV) file. For example, you could open the CVS file in Microsoft Excel and sort the list of alerts by Severity and then Date Created.