Important
Microsoft Defender for Business is now in preview, and will roll out gradually to customers and IT Partners who sign-up here to request it. We will onboard an initial set of customers and partners in the coming weeks and will expand the preview leading up to general availability. Note that preview will launch with an initial set of scenarios, and we will be adding capabilities regularly.
Some information in this article relates to prereleased products/services that might be substantially modified before they are commercially released. Microsoft makes no warranties, express or implied, for the information provided here.
After your setup and configuration process is complete for your company, the best way to get started using Microsoft Defender for Business (preview) is by visiting your Microsoft 365 Defender portal (https://security.microsoft.com), and signing in with your user account for Microsoft 365.
Navigate the Microsoft 365 Defender portal
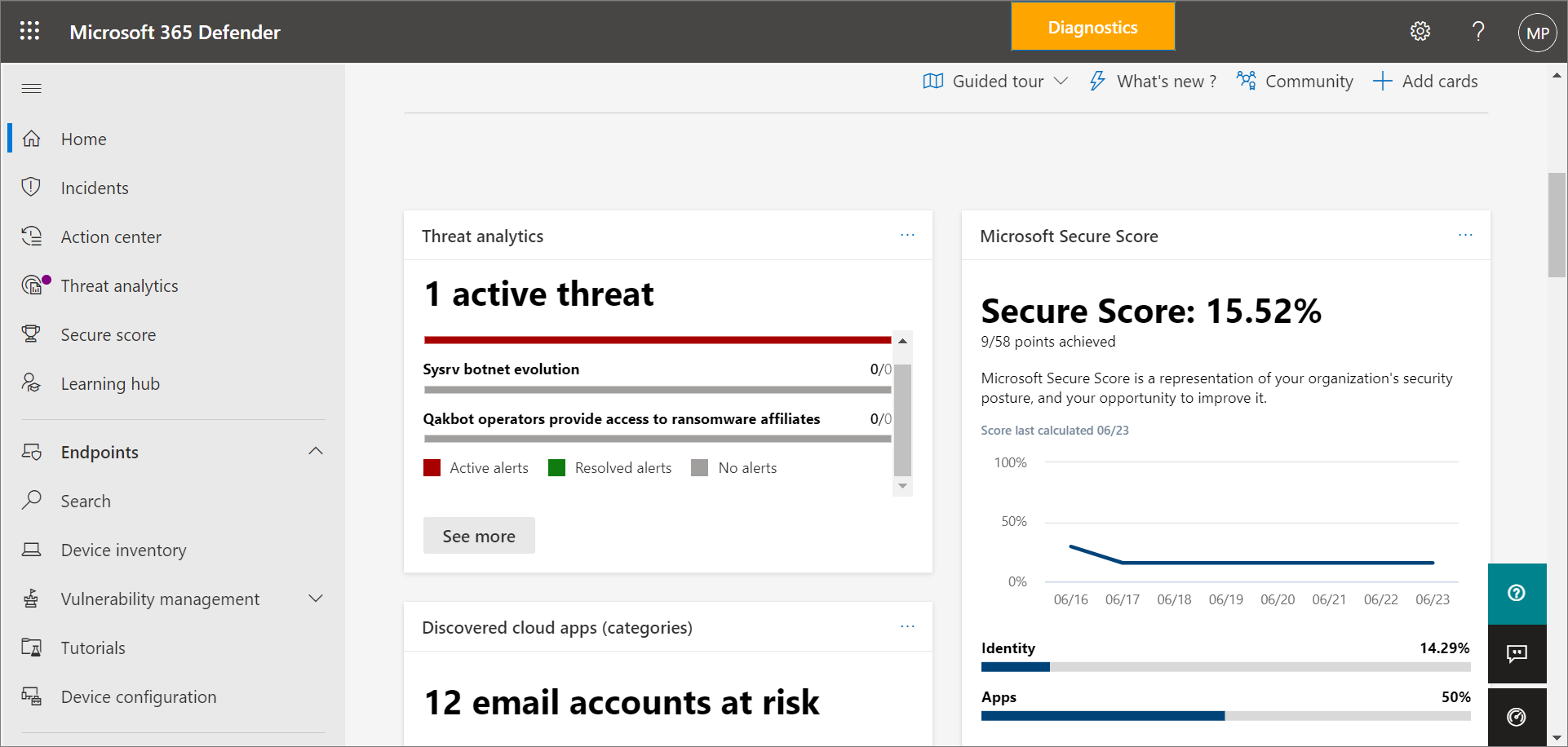
The Microsoft 365 Defender portal (https://security.microsoft.com) is your one-stop shop for using and managing Microsoft Defender for Business (preview). It includes a welcome banner and callouts to help you get started, cards that surface relevant information, and a navigation bar to give you easy access to the various features and capabilities.
Take a moment to get acquainted with your Microsoft 365 Defender portal.
Use the navigation bar
Use the navigation bar on the left side of the screen to access your incidents, view reports, and manage your security policies and settings. The following table describes items you’ll see in your navigation bar.
| Item | Description |
|---|---|
| Home | Takes you to your home page in Microsoft 365 Defender. The home page includes cards that highlight any active threats that were detected, along with recommendations to help secure your company’s data and devices.
Recommendations are included in Defender for Business (preview) can save your security team time and effort. Recommendations are based on industry best practices. To learn more about recommendations, see Security recommendations – threat and vulnerability management. |
| Incidents | Takes you to your list of recent incidents. As alerts are triggered, incidents are created. An incident can include multiple alerts. Make sure to review your incidents regularly.
To learn more about incidents, see View and manage incidents in Microsoft Defender for Business (preview). |
| Action center | Takes you to your list of response actions, including completed or pending actions. – Select the History tab to see the actions that were taken. Some actions are taken automatically; others are taken manually or complete after they are approved. – Select the Pending tab to view actions that require approval to proceed. To learn more about the Action center, see Review remediation actions in the Action center. |
| Threat analytics | Takes you to a view of current threats, and provides you with an at-a-glance view of your threat landscape. Threat analytics also includes reports and information from Microsoft security researchers.
To learn more about threat analytics, see Track and respond to emerging threats through threat analytics. |
| Secure score | Provides you with a representation of your company’s security position and offers suggestions to improve it.
To learn more about Secure Score, see Microsoft Secure Score for Devices. |
| Learning hub | Provides access to security training and other resources through learning paths that are included with your subscription. You can filter by product, skill level, role, and more. The Learning hub can help your security team ramp up on security features & capabilities in Defender for Business (preview) and more Microsoft offerings, such as Microsoft Defender for Endpoint and Microsoft Defender for Office 365. |
| Endpoints > Search | Enables you to search for one or more devices that were onboarded to Microsoft Defender for Business (preview). |
| Endpoints > Device inventory | Enables you to search for one or more devices that were onboarded to Microsoft Defender for Business (preview). |
| Endpoints > Vulnerability management | Provides you with a dashboard, recommendations, remediation activities, a software inventory, and a list of potential weaknesses within your company. |
| Endpoints > Tutorials | Provides access to walkthroughs and simulations to help you learn more about how your threat protection features work.
Select the Read the walkthrough link before attempting to get the simulation file for each tutorial. Some simulations require Office apps, such as Microsoft Word, to read the walkthrough. |
| Endpoints > Device configuration | Lists your security policies by operating system and by type.
To learn more about your security policies and settings, see View or edit policies in Microsoft Defender for Business (preview). |
| Reports | Lists your available security reports. These reports enable you to see your security trends, view details about threat detections and alerts, and learn more about your company’s vulnerable devices. |
| Health | Enables you to view your service health status and plan for upcoming changes. – Select Service health to view the health status of the Microsoft 365 services that are included in your company’s subscription. – Select Message center to learn about planned changes and what to expect. |
| Permissions & roles | Enables you to assign permissions to the people in your company who will be managing your security and viewing incidents and reports in the Microsoft 365 Defender portal. Also enables you to set up and manage device groups to onboard your company’s devices and assign your threat protection policies. |
| Settings | Enables you to edit settings for the Microsoft 365 Defender portal and Microsoft Defender for Business (preview). For example, you can onboard (or offboard) and your company’s devices (also referred to as endpoints). You can also define rules, such as alert suppression rules, and set up indicators to block or allow certain files or processes. |
| More resources | Navigate to other portals, such as Azure Active Directory. Keep in mind that the Microsoft 365 Defender portal should meet your needs without requiring you to navigate to other portals. |
Complete a learning module about incidents and response actions
See the learning module, Detect and respond to security issues, to get an overview of incidents and response actions. You’ll learn about the incident queue, alerts, and response actions that you can take. This course will help you get started working with incidents in Defender for Business (preview).
Note
Although the learning module (Detect and respond to security issues) is actually for Microsoft Defender for Endpoint, the basic concepts and overall flow are similar to what you’ll see in Defender for Business (preview).

